G K GUJAR MEMORIAL CHARITABLE TRUST'S
DR. ASHOK GUJAR TECHNICAL INSTITUTE'S
Principal : Dr. Anwar M. Mulla
Principal, Dr. Daulatrao Aher College of Engineering, Karad
Prof. Hanmant M. Kumbhar
Vice Principal, Dr. Daulatrao Aher College of Engineering, Karad
Head of Department : Mr. Ashish N. Patil
Assistant Professor, Head of Computer Science & Engineering department, Dr. Daulatrao Aher College of Engineering, Karad
Coordinator : Ms. Sumalatha Dhanraj Bandari
Assistant Professor, Department of Computer Science & Engineering, Dr. Daulatrao Aher College of Engineering, Karad
Ms. Sayali P. Shinde, Assistant Professor, Department of Computer Science & Engineering, Dr. Daulatrao Aher College of Engineering, Karad
|
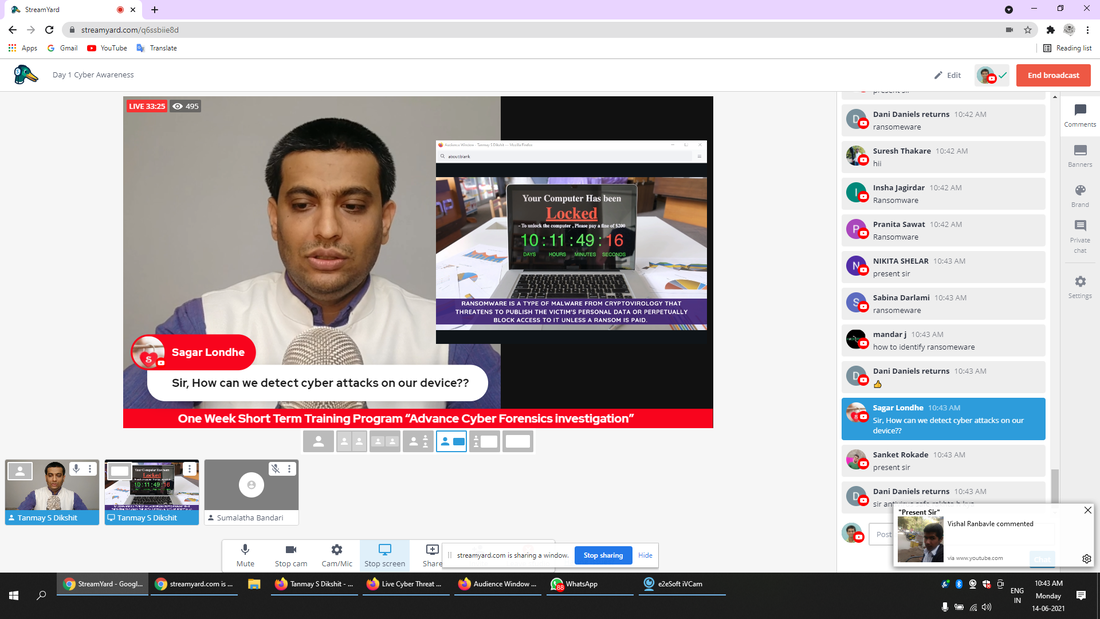
Day 1 Awareness
|
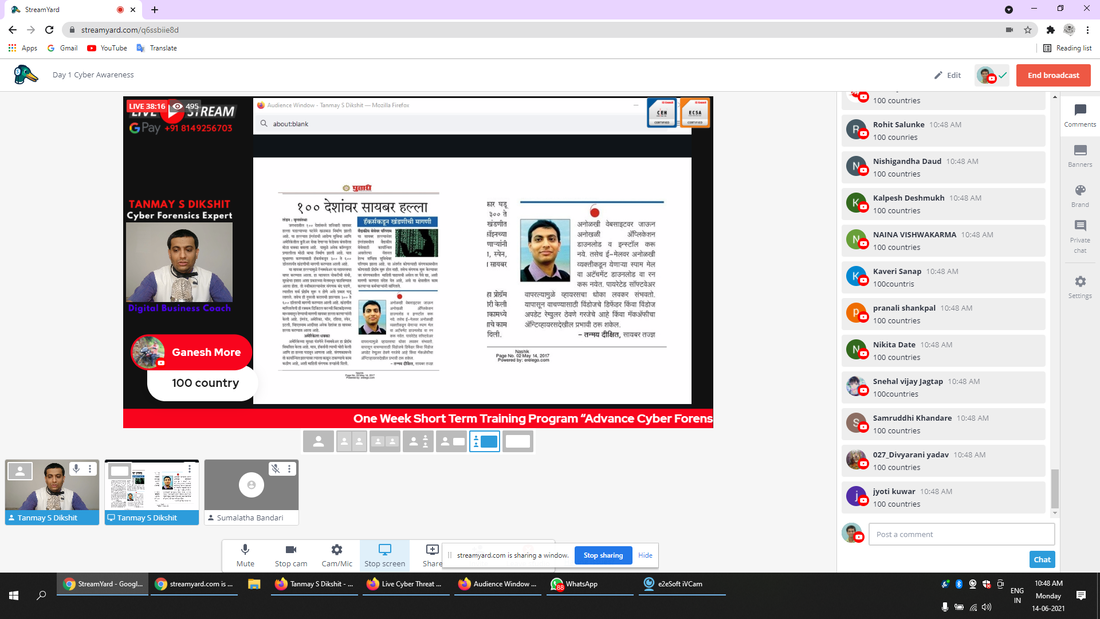
Day 2 Techniques
|
Day 3 Security
|
Day 4
Affiliate System Day 5
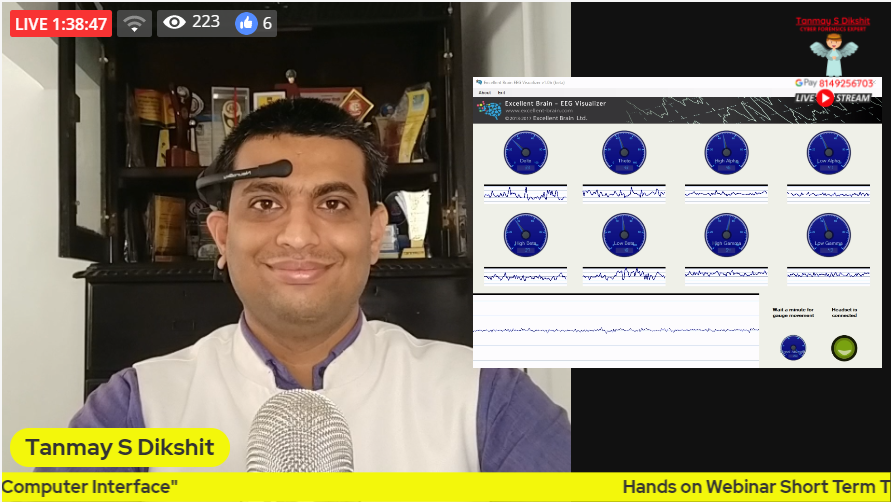
Brain Computer Interface |
Download Tutorials Files
|
|
|
| ||||||||||||||||||||||||
Download Software
|
|
|
| ||||||||||||||||||||||||
|
|
| ||||||||||||||||||
https://www.qfxsoftware.com |
http://whois.domaintools.com |
Download Presentation
|
|
| ||||||||||||||||||